Easy & Intuitive secrets management
for teams of any size.
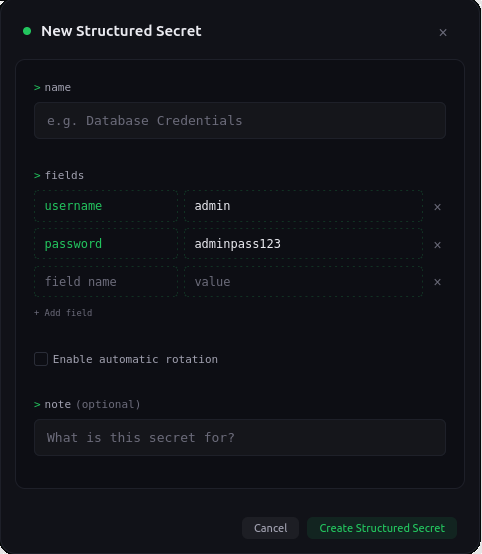
Structured multi-field secrets
Store credentials as structured objects with named fields. Access individual fields via SDK or CLI without parsing JSON. Each field is independently addressable and can be configured to auto-rotate while others stay static.
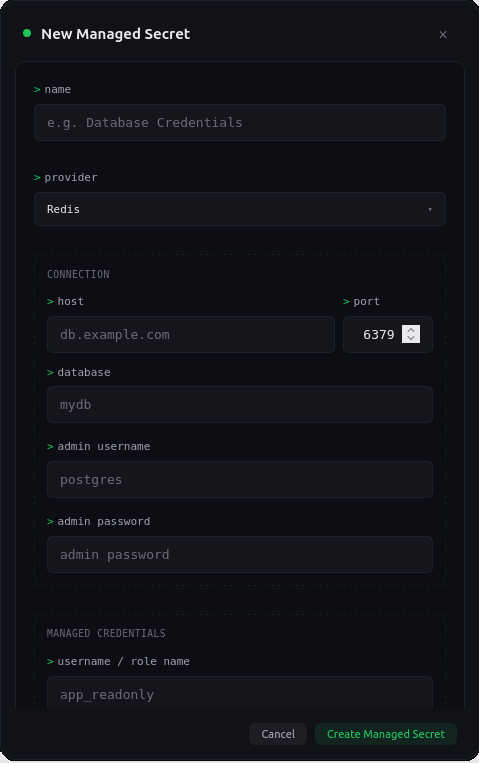
Managed database credentials
SikkerKey rotates your database password on a schedule and pushes it to your database automatically. A CLI agent runs next to your database, applies the new credentials, and reports its health back to the dashboard. Your database is never exposed to the internet.
PostgreSQL, MySQL, Redis, and MongoDB.
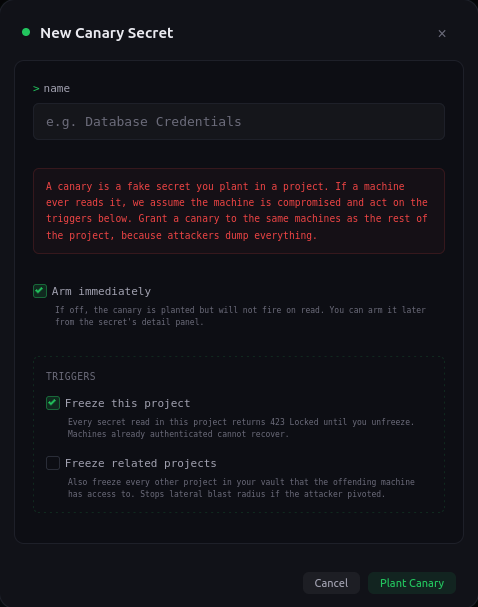
Canary secrets that auto-freeze on read
Plant a decoy secret in any project. It looks identical to a real credential, but reading it triggers a silent containment: the project freezes, every subsequent request returns 423 Locked, and you get a critical alert with the offending machine, IP, and timestamp. The attacker still receives the canary value on that read, so they never know they tripped anything. Optional related-project freeze contains lateral movement when the offending machine has access to other projects in your vault.
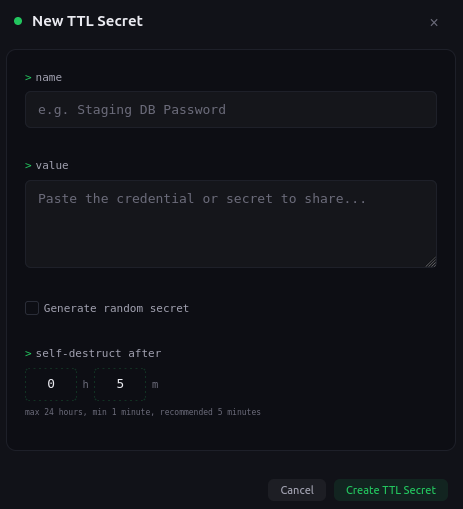
Temporary self-destructing secrets
Share credentials without pasting them into Slack or email. Create a secret with a self-destruct timer, get a one-time link and passphrase. The recipient enters the passphrase to view the value. Wrong passphrase? Destroyed. Correct passphrase? Destroyed after viewing. Expired? Destroyed. One attempt. No traces.
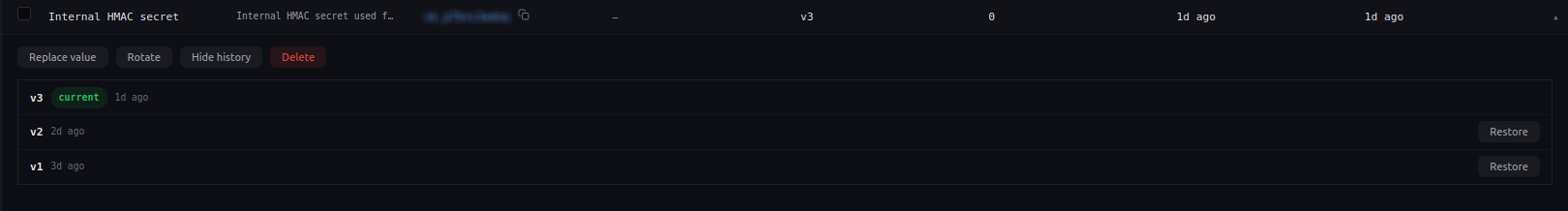
Version history and rollback
Every change creates a new encrypted version. Browse the full history, see when each version was created, and restore any previous version instantly. Your team can roll back a bad deploy in seconds.
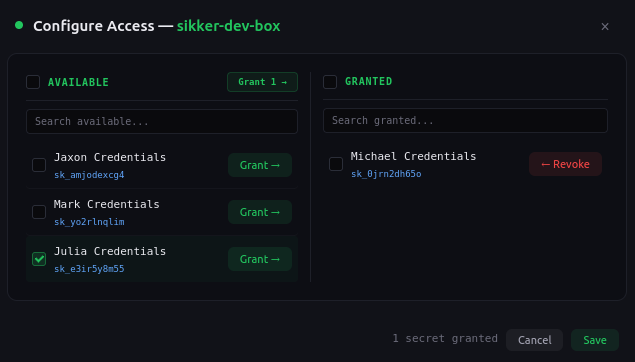
Per-secret machine access
Machines authenticate with Ed25519 signatures on every request. No tokens to leak, no sessions to hijack. Grant access to individual secrets, not entire projects. Revoke instantly from the dashboard.
Everything else you need
Built for teams that take secrets seriously.
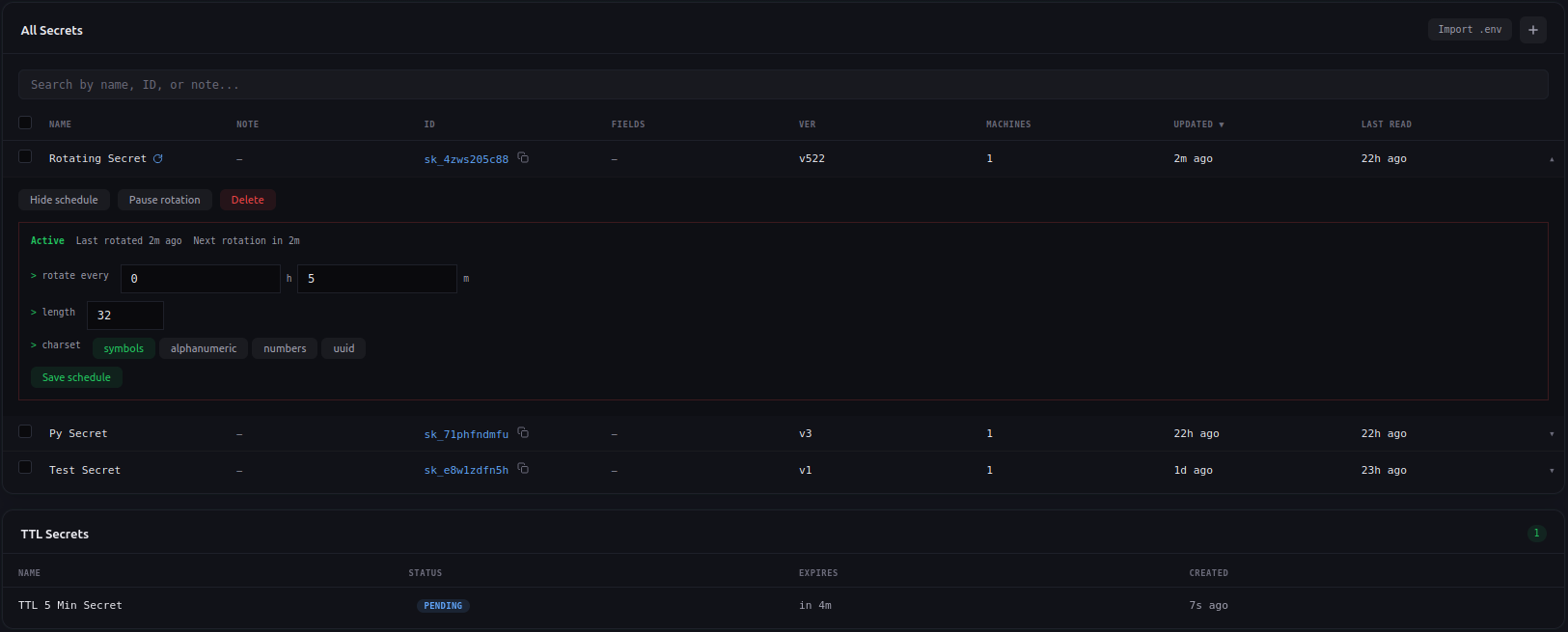
Automatic rotation
Enable rotation on any secret or structured secret. Set the interval, charset, and length. For structured secrets, choose which fields rotate while others stay static.
Severity-tagged audit log
Every operation logged with severity. Filter by action, user, machine, IP, or time. Export to CSV. Real-time email alerts for critical events.
Team collaboration
Invite team members to your vault. Control per-project, per-action permissions. Team members get scoped access without managing encryption keys.
CLI and 5 SDKs
Single-binary Go CLI. Kotlin, Go, Python, Node.js, and .NET SDKs. Bootstrap a machine in one command, read secrets in one line of code.
30-day trash retention
Deleted secrets are soft-deleted and retained for 30 days. Restore accidentally deleted secrets or permanently purge them.
Project-based encryption
Each project has its own randomly generated master key and independent encryption. Compromising one project reveals nothing about another.
Stop storing secrets in plaintext.
Create a free vault in under a minute. No credit card required.
Start for Free