Identity that expires with the workload.
CI runners, autoscaled nodes, preview environments, batch jobs. Each one self-enrolls, gets its own Ed25519 identity, reads exactly the secrets you've scoped it to, and expires on its own. Configure the policy once, provision machines at any scale.
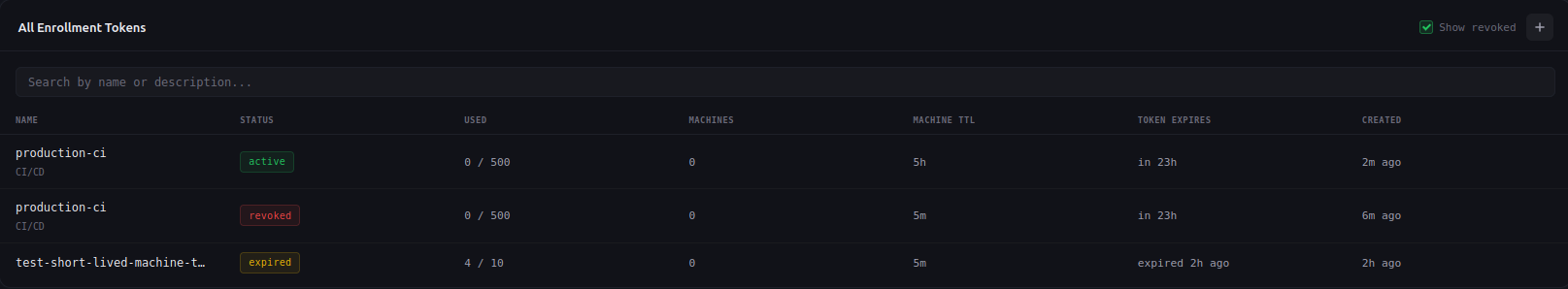
One token, thousands of machines
An enrollment token is a reusable policy template. You set the projects, the secrets, the machine lifetime, and the maximum uses once. Every machine that runs the enrollment command inherits the same scope without any dashboard interaction.
curl -sSL https://api.sikkerkey.com/v1/<vault>/enroll/<token> | shLinux, macOS, and Windows (PowerShell). Each enrollment generates a fresh Ed25519 keypair locally, registers the public key with SikkerKey, and writes the identity file to ~/.sikkerkey/vaults/{vaultId}/.
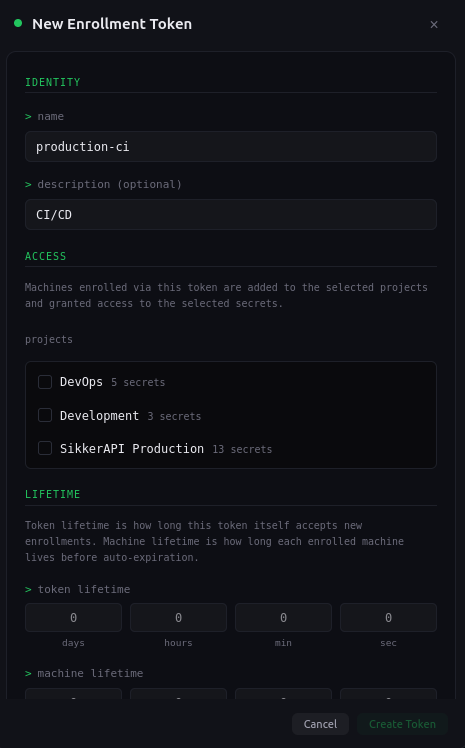
Machine lifetime baked in
Every ephemeral machine is stamped with an expiration timestamp at enrollment time. When the timestamp passes, authentication is refused and the machine is auto-disabled by a background sweep within one minute. After a 30-day retention window the row is permanently deleted.
No cleanup scripts. No zombie identities sitting in the dashboard weeks after the workload ended. The audit trail is preserved for the retention window so you can always answer “what did this machine do while it was alive.”
Docs →expiresAtScoped at the token, enforced on enrollment
The token encodes which projects a machine joins and which secrets it can read. An ephemeral machine cannot read anything outside that scope. The same per-secret access grants and Ed25519 signature requirements apply as for any other machine.
If a referenced project or secret has been deleted, enrollment fails cleanly without consuming a token slot and without creating a partially-configured machine.
Docs →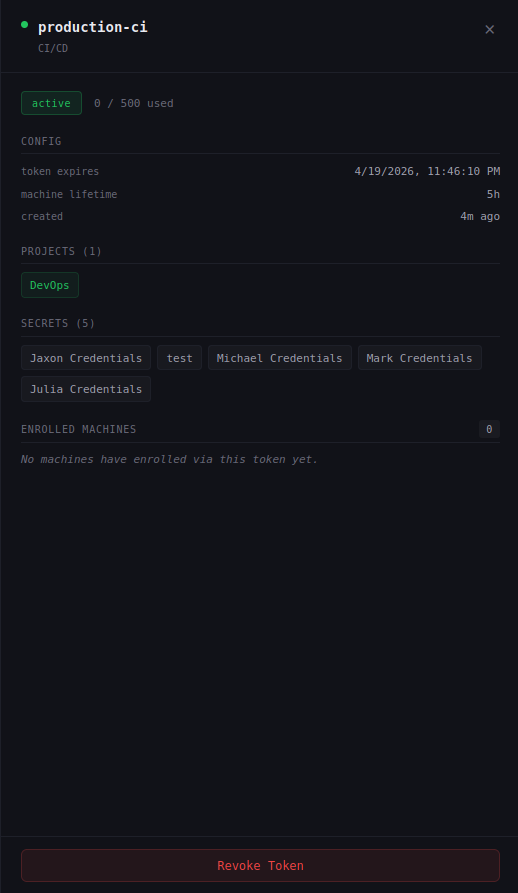
Optional guardrails on who can enroll
Bind the token to a source CIDR so enrollments are accepted only from your known network range. Require the enrolling machine's hostname to match a regex. Auto-assign machine names from a template like ci-{uuid8} so every ephemeral machine gets a unique identifier without a human naming it.
All guardrails are evaluated atomically before a token slot is consumed, so a failed check never depletes your enrollment budget.
Docs →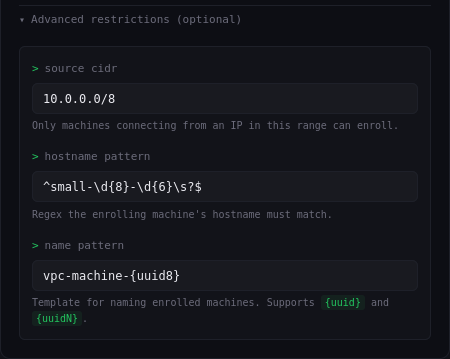
Full SikkerKey security model on every request
Enrollment doesn't skip any part of the auth pipeline. Every request from an ephemeral machine is Ed25519-signed, nonce-protected against replay, checked against your IP allowlist if enabled, and recorded in the audit log attributed to that specific machine.
Per-machine audit means every secret read is logged against the unique ephemeral identity that made it, not a shared service identity. You can trace exactly which CI job read which credential at which moment.
Docs →Built for fleets that move
Every detail matters when machines come and go on their own.
Automatic lifecycle
Soft-expire at TTL, 30-day retention for audit continuity, then hard-delete. No manual cleanup required at any stage.
Instant token revocation
Revoke an enrollment token and all future enrollments fail immediately. Live machines continue under their own TTL, which you can also cut short per machine.
Per-machine audit attribution
Every secret read is logged against the individual ephemeral identity that made it, never a shared or pooled credential.
Rate-limited enrollment
30 enrollments per hour per source IP at the public endpoint. A leaked token cannot be hammered into mass-enrolling.
Real-time dashboard
New ephemeral machines, revocations, and expirations stream to the dashboard via SSE. No refresh needed to see the fleet change.
Plan-gated, usage-tracked
Available on Pro and Enterprise. Enrolled machines count against your plan limit; plan-denied enrollments do not consume token slots.
Ephemeral fleets deserve ephemeral identity.
Create your first enrollment token in under a minute. Available on Pro.
Start for Free